Yorubaboy
Thread Starter
Member
- Local time
- Today 1:27 AM
- NaijaCash
- 0
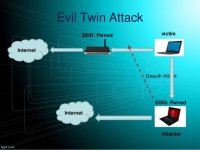
During an evil twin attack, a hacker tricks victims, and they log in to a stolen and insecure form of WiFi. Once the victims connect, the hacker can see everything they do online.
Setting up an evil twin network is remarkably easy. Several off-the-shelf products allow anyone to become a hacker, including people who don't know anything about computers or programming.
Evil twin attacks, step by step
Hackers need impatient web users to pull off an evil twin attack. Unfortunately, plenty of us fall into this category. When we go into a public space, such as a library or a coffee shop, we expect that establishment to offer free and fast WiFi. In fact, reporters even rank businesses by their connection speeds.But that speed and convenience come with a cost. Hackers can quickly take over a safe-seeming WiFi connection and see (or steal) anything users do online.
An attack typically works like this:
- Step 1: Set up an evil twin access point.
A hacker looks for a location with free, popular WiFi. The hacker takes note of the Service Set Identifier (SSID) name. Then, the hacker uses a tool like a WiFi Pineapple to set up a new account with the same SSID. Connected devices can't differentiate between legitimate connections and fake versions. - Step 2: Set up a fake captive portal.
Before you can sign in to most public WiFi accounts, you must fill in data on a generic login page. A hacker will set up an exact copy of this page, hoping that they will trick the victim into offering up authentication details. Once the hacker has those, they can log in to the network and control it. - Step 3: Encourage victims to connect to the evil twin WiFi.
The hacker moves close to victims and makes a stronger connection signal than the valid version. Anyone new will only see the evil twin, and they will tap and log in. The hacker can kick off anyone currently connected with a distributed denial of service (DDoS) attack, which temporarily takes the valid server offline and prompts mass logins. - Step 4: The hacker steals the data.
Anyone who logs in connects via the hacker. This is a classic man-in-the-middle attack, which allows the attacker to monitor anything that happens online. If the user logs into something sensitive (like a bank account), the hacker can see all the login details and save them for later use.
Evil twin attacks: 2 examples
Why would someone want to sit between customers and websites? Let's walk through two examples of how hackers might use data like this.Let's imagine a hacker sitting inside a connection at a local coffee shop:
- The setup is successful. The hacker has created an evil twin network, and one person logs in.
- The attack begins. The victim has no idea that the connection is not secure. They head to a banking page and log in. They then agree to transfer $100 to a friend.
- The hacker transforms the data. The hacker intercepts the request and changes the recipient to an account that they own. The bank processes the transaction and sends a receipt. The hacker changes that receipt, so the victim thinks the back just completed the original work.
- The setup is successful. The hacker has created an evil twin network, along with a phishing site.
- The connection initiates. The victim must log in to this phishing site to gain access. The person might believe they're logging into a common site, like Facebook or Google. But instead, they're connecting with a hacker.
- The hacker steals the target data. The hacker can see the victim's login data and save it. The hacker can use that login to steal funds, or the hacker can sell credentials to buyers on the black market.
- The hacker releases the victim. The hacker disconnects the victim. The next login is valid, and the victim has no idea anything went wrong.
Prevent the next attack
More than 80 percent of people will connect to any WiFi network available to them when they're out and about. If you're part of this population, it's time for a new strategy.The quickest and easiest way to stay safe is to avoid any public WiFi connection. Rely on your own cell service or wait until you're at home or in your office to connect.
If you must connect via public WiFi, follow these three steps:
- Use VPN. A virtual private network encrypts data as it passes between your device and a network. A system like this can keep you safe, even if you're dealing with a hacker.
- Turn off autosaves. Your device may seek out WiFi connections you've made in the past and connect again, even if you don't ask for the help. Turn off this option so you can be mindful about your use.
- Be judicious. If you log in to a WiFi system without using a VPN, be careful about the logins you use. Don't tap into your bank account or work servers. But if you absolutely must look at Twitter, and you can accept the risks, do so.

